Technology companies are locked in a seemingly-endless tussle with cybercriminals when it comes to the evolution of security protocols. Website and device developers will install a new safety feature, only for hackers to quickly devise a way to exploit it. Recent innovations like two-factor authentication have proven solid so far, but it looks as though the security industry will move past this in the near future. Identity recognition software is swiftly becoming commonplace on mobile devices, and this could soon be the standard for anything that requires users to input sensitive information.
Security is of the utmost concern for internet users
Internet security is one of the most important things that users look out for, with awareness about the sheer levels of cyber-attacks on the rise. Statistics show that over 18 million sites are infected with malware at any given time. More shockingly, 90 percent of financial institutions reported that they had been targeted by malicious attacks in 2018. These figures are well known by the internet community, and people are more cautious than ever about where they input their information.
Businesses are aware of this desire of consumers to use sites that are safe and secure. This is why security protocols have helped become a major selling point for new companies. According to authoritative casino sites, safety and security is the first thing that they look for when recommending a new casino. They aim to ensure that each site is protected with the latest SSL encryption technology.
Other sites that require users to input information regarding their finances also have to go above and beyond to ensure that they are safe and secure. PayPal is a good example of a company that has done this, and it has earned a solid reputation by having very few data breaches in its history. Most of these sites already boast encryption software and two-factor authentication, but they are always striving to improve the protocols they have in place.
Touch and face recognition growing on mobile
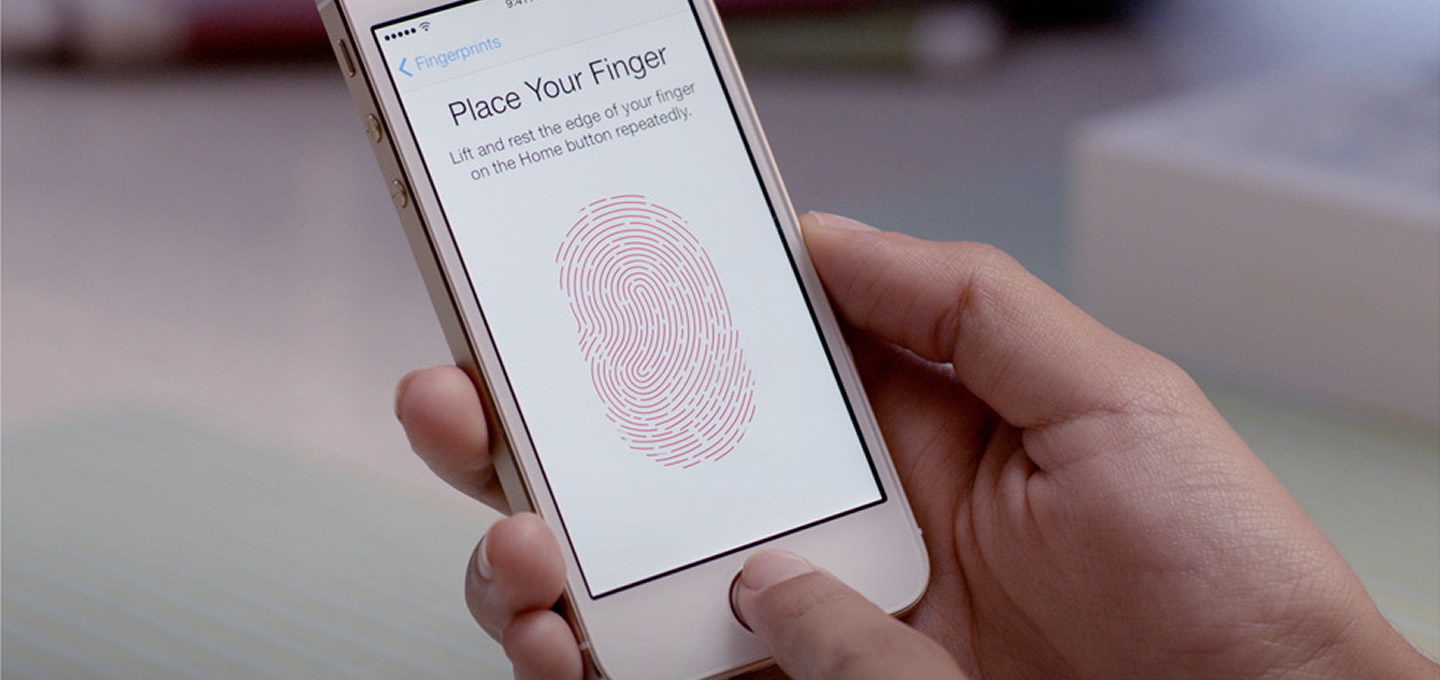
Smartphones and tablets have tested various security protocols over the years, with options like pattern drawing and pin codes having been particularly effective. Newer models, though, are going beyond these procedures. On recent devices from leading mobile developers, touch ID and facial recognition are becoming more commonplace.
Fingerprint scanners have been around on mobile for a while, but they have had mixed success when they have been located on the actual screen. Because this method isn’t completely reliable, Apple has devised a new form of touch security. Now, the unlock button on the latest range of iPads has a nifty touch finger scan option which works incredibly well. Not only is this used for unlocking the device securely, but users are also prompted to touch the button to confirm purchases. This means that it is impossible for unauthorised users to spend money using the device. It also ensures that things can’t be bought by accident.
Facial recognition software operates on the same principles. This has been around for some time as well, but it has taken a few generations for it to be considered as one of the top forms of security. The software used to unlock devices such as the latest iPhones and the iPad Pro is extremely reliable and works well.
With touch and facial recognition on Apple devices reaching an almost infallible level, it will most likely be used as the main security protocol on all mobile devices moving forward. Online businesses that require users to make transactions could use this software to their advantage. Whenever anyone wants to top up funds online, they would have to touch their fingerprint or scan their face to do so. Hackers would have a tough time overcoming this.