Has China found a way to spy on computers used by the world’s top tech firms and perhaps even the US government by implanting them with tiny secret microchips? That’s what was alleged in a recent article from Bloomberg Businessweek, which claimed the US is investigating some form of spy microchip thought to have been inserted into Chinese-made circuit boards used by a company that produces video data servers. Its products have, according to Bloomberg, been purchased by Apple, Amazon and many other large firms, as well as the US departments of Defense and Homeland Security, Congress and NASA.
If proved true, these allegations would have huge implications for all the parties involved, as well as global security, trade and international relations. But the supplier of the allegedly hacked hardware, the companies that bought it, and the Chinese government have repeatedly and strenuously denied that the chips exist or that any server hardware was compromised. US and UK officials have backed the denials, while the FBI has stated that it is their policy “to neither confirm nor deny the existence of an investigation”.
The problem is that, at this stage, it’s impossible to know who’s telling the truth. The chip described in the report is said to be disguised as an extremely small and otherwise unremarkable electronic component. Proving that it even exists, let alone what it does, would require careful reverse engineering and security analysis by somebody with access to the allegedly afflicted hardware.
Security technology researchers I have consulted are adopting a “wait and see” attitude until more information emerges. Bloomberg’s story relies entirely on unnamed sources. Until somebody comes forward with a credible and detailed technical report, there is little to be gained by speculating about this specific incident. But if it were true, the nature of the incident would make it very difficult for authorities to respond.
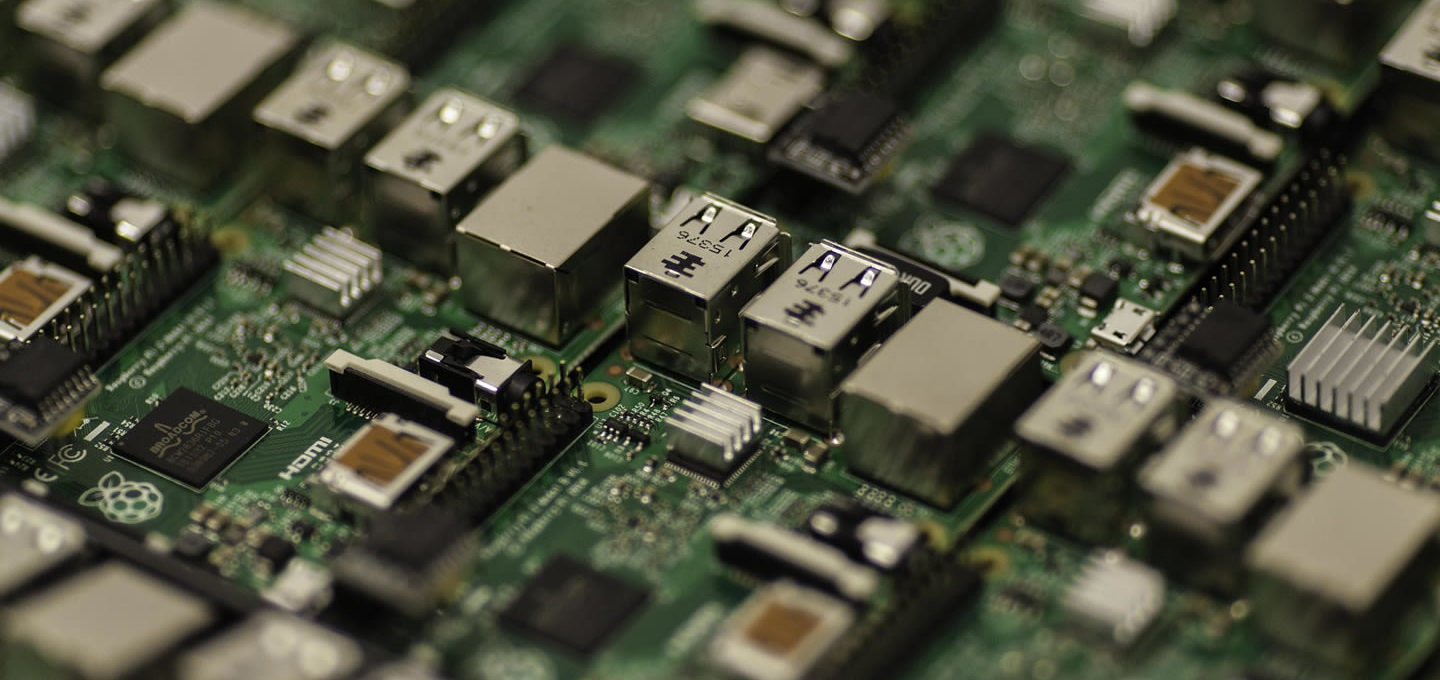
The alleged attack quickly captures the imagination because it highlights a well-known challenge in cybersecurity: maintaining the integrity of end-point hardware. End-point hardware in this context simply means any device used to transmit or receive electronic messages. This can include obvious items like smartphones, laptops and servers, but also the growing body of Internet of Things devices such as smart home appliances, self-driving cars and connected industrial machinery.
If an attacker gains physical access to an end-point device, this can subvert multiple layers of security. A well-known example was publicised in 2013 when a criminal gang installed covert “KVM switches” onto computers in London bank branches. These simple and inexpensive pieces of equipment let attackers monitor what a computer is doing and then operate it remotely. In this way, accessing the physical equipment effectively gets around a variety of protective measures.
The chips described in the Bloomberg article are a much more technologically sophisticated example of the same basic idea. In this case, it is alleged that the offending hardware is a specially designed chip the size of a grain of rice, manufactured and distributed at a large scale.
If it were to emerge that these chips do exist and work as described, the next challenge would be the “attribution” problem – demonstrating who was responsible for creating and installing them. This is critical for anyone who wants to respond to a cyber-attack using legal, diplomatic, or military action, but it remains extremely difficult due to limited forensic methods available.
Legal action
If a government was able to prove an attack like this was carried out by another state, there are a range of responses available. A conspiracy to install and operate a system of this type would constitute a crime under the domestic laws of most states. Jurisdictions such as the US and UK could attempt to prosecute people involved in this kind of conspiracy using laws that criminalise unauthorised access to a computer and interception of communications, among others.
But any such criminal prosecution would face three significant hurdles. You would need to identify and indict the suspects involved in the conspiracy and physically arrest or extradite them. You’d then have to present enough evidence to persuade a jury of guilt beyond reasonable doubt.
In recent years, US law enforcement officials have announced criminal indictments of individuals accused of international cyber-espionage. But there is no realistic prospect that any of the accused parties, as employees of a state security agency, would be extradited to face charges in a US court. Instead, it is widely believed that such public announcements are designed signal awareness of state cyber-operations and potentially to deter such operations.
If domestic law provides little hope of action, what about international law? Even if overwhelming evidence is produced to demonstrate that the chips exist and that the Chinese government directed their deployment, as a legal matter there is nothing to suggest that these actions actually constitute a “cyber-attack” as that term is used in international law
There is a sharp distinction between state acts of violence, and non-violent espionage or psychological (propaganda) operations. Principles of international law require that any state response should be proportional and therefore limited in this case to non-violent options such as a diplomatic complaint or economic sanctions.
Nothing in the reporting suggests an outbreak of actual cyber war. At worst, what we see is the latest chapter in a still developing, complex, and poorly understood cyber “cold war”.![]()
Robert Carolina, Executive Director, Institute for Cyber Security Innovation, Royal Holloway
This article is republished from The Conversation under a Creative Commons license. Read the original article.
Photograph by Pexels